[Update Nov 2022] CyberOps Professional 300-215 dumps with PDF and VCE
New updated CyberOps Professional 300-215 dumps with the PDF download file and VCE mock exam engine, 59 newly updated exam questions, and answers, verified by CyberOps Professional experts to ensure validity.
Download CyberOps Professional 300-215 dumps: https://www.leads4pass.com/300-215.html Practice the complete exam questions to help you easily pass the 300-215 CBRFIR certification exam.

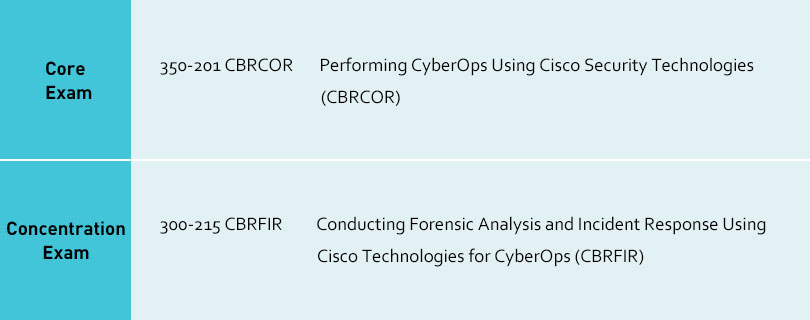
Candidates for the Cisco Certified CyberOps Professional certification need to meet two conditions. I have provided the 300-215 CBRFIR exam materials above. You should first complete the first step and take the core exam (350-201 CBRCOR), Candidates can download 350-201 dumps here: https://www.leads4pass.com/350-201.html (139 Q&A). Get the complete Cisco Certified CyberOps Professional dumps to help you complete the target certification exam.
The 300-220 CBRTHD certification exam will be launched on December 2, 2022, currently, you can only choose the 1+1 mode to get the complete Cisco Certified CyberOps Professional certification: (350-201 CBRCOR, 300-215 CBRFIR).
» Read more about: [Update Nov 2022] CyberOps Professional 300-215 dumps with PDF and VCE »