
The Cisco 200-201 CBROPS Certification Exam Plans I am going to talk about next come from the stories of many exam winners who passed the 2023 certification exam!
Whether you’re a novice or a candidate who has taken multiple certification exams, get inspired here as you take the 2023 200-201 exam!
Everyone knows that Cisco certification exams are very professional, including the 200-201 certification exam!
Statistics from the experience of many successful people:
1. Using the Cisco 200-201 exam book, the success rate of passing the exam is about 65%, and it takes 1-2 months.
2. The success rate of participating in online training is about 76%, and it takes about 4 weeks.
3. The success rate is about 45% through self-study and using free materials, and it takes about 1-2 months.
4. Using the Cisco 200-201 exam practice materials, namely 200-201 dumps: https://www.leads4pass.com/200-201.html, the success rate is about 90%, and it takes 1-2 weeks.
5. Other
In summary, it is clear at a glance!
So candidates can choose their favorite learning method according to the current learning situation because each method has success! But here I highly recommend Lead4Pass 200-201 dumps! Compared to other it providers, Lead4Pass The prices are even better, so why not choose a provider with the longest history and good value for money?
More importantly! Share part of Lead4Pass 200-201 dumps for free online download: https://drive.google.com/file/d/1cK4ha35Hi3v8NNZ2k2t0H7N4rK5lrozB/
You can also practice part of the Lead4Pass 200-201 dumps online
| Type | Number of exam questions | Exam name | Exam code | Answers |
| Free | 15 | Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) | 200-201 | View |
Question 1:
What is obtained using NetFlow?
A. session data
B. application logs
C. network downtime report
D. full packet capture
Question 2:
What is the impact of encryption?
A. Confidentiality of the data is kept secure and permissions are validated
B. Data is accessible and available to permitted individuals
C. Data is unaltered and its integrity is preserved
D. Data is secure and unreadable without decrypting it
Question 3:
What is a description of a social engineering attack?
A. fake offer for free music download to trick the user into providing sensitive data
B. package deliberately sent to the wrong receiver to advertise a new product
C. mistakenly received valuable order destined for another person and hidden on purpose
D. email offering last-minute deals on various vacations around the world with a due date and a counter
Question 4:
An organization is cooperating with several third-party companies. Data exchange is on an unsecured channel using port 80 Internal employees use the FTP service to upload and download sensitive data An engineer must ensure confidentiality while preserving the integrity of the communication. Which technology must the engineer implement in this scenario\’?
A. X 509 certificates
B. RADIUS server
C. CA server
D. web application firewall
Question 5:
An analyst is investigating an incident in a SOC environment. Which method is used to identify a session from a group of logs?
A. sequence numbers
B. IP identifier
C. 5-tuple
D. timestamps
Question 6:
What is the difference between a threat and a risk?
A. Threat represents a potential danger that could take advantage of a weakness in a system
B. Risk represents the known and identified loss or danger in the system
C. Risk represents the nonintentional interaction with uncertainty in the system
D. Threat represents a state of being exposed to an attack or a compromise, either physically or logically.
A threat is any potential danger to an asset. If a vulnerability exists but has not yet been exploited–or, more importantly, it is not yet publicly known–the threat is latent and not yet realized.
Question 7:
What is the function of a command and control server?
A. It enumerates open ports on a network device
B. It drops secondary payload into malware
C. It is used to regain control of the network after a compromise
D. It sends instructions to a compromised system
Question 8:
A security engineer notices confidential data being exfiltrated to a domain “Ranso4134- mware31-895” address that is attributed to a known advanced persistent threat group The engineer discovers that the activity is part of a real attack and not a network misconfiguration. Which category does this event fall under as defined in the Cyber Kill Chain?
A. reconnaissance
B. delivery
C. action on objectives
D. weaponization
Question 9:
Which two elements of the incident response process are stated in NIST Special Publication 800-61 r2? (Choose two.)
A. detection and analysis
B. post-incident activity
C. vulnerability management
D. risk assessment
E. vulnerability scoring
Reference: https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-61r2.pdf
Question 10:
Which tool provides a full packet capture from network traffic?
A. Nagios
B. CAINE
C. Hydra
D. Wireshark
Question 11:
Which technology should be used to implement a solution that makes routing decisions based on HTTP header, uniform resource identifier, and SSL session ID attributes?
A. AWS
B. IIS
C. Load balancer
D. Proxy server
Load Balancing: HTTP(S) load balancing is one of the oldest forms of load balancing. This form of load balancing relies on layer 7, which means it operates in the application layer.
This allows routing decisions based on attributes like HTTP header, uniform resource identifier, SSL session ID, and HTML form data.
Load balancing applies to layers 4-7 in the seven-layer Open System Interconnection (OSI) model. Its capabilities are L4. Directing traffic based on network data and transport layer protocols, e.g., IP address and TCP port. L7.
Adds content switching to load balancing, allowing routing decisions depending on characteristics such as HTTP header, uniform resource identifier, SSL session ID, and HTML form data. GSLB. Global Server Load Balancing expands L4 and L7 capabilities to servers in different sites
Question 12:
Refer to the exhibit.
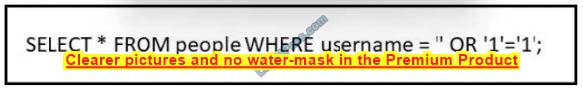
Which type of attack is being executed?
A. SQL injection
B. cross-site scripting
C. cross-site request forgery
D. command injection
Reference: https://www.w3schools.com/sql/sql_injection.asp
Question 13:
What is the difference between the ACK flag and the RST flag?
A. The RST flag approves the connection, and the ACK flag terminates spontaneous connections.
B. The ACK flag confirms the received segment, and the RST flag terminates the connection.
C. The RST flag approves the connection, and the ACK flag indicates that a packet needs to be resent
D. The ACK flag marks the connection as reliable, and the RST flag indicates the failure within TCP Handshake
Question 14:
What is the difference between inline traffic interrogation (TAPS) and traffic mirroring (SPAN)?
A. TAPS interrogation is more complex because traffic mirroring applies additional tags to data and SPAN does not alter the integrity and provides a full-duplex network.
B. SPAN results in more efficient traffic analysis, and TAPS is considerably slower due to latency caused by mirroring.
C. TAPS replicates the traffic to preserve integrity, and SPAN modifies packets before sending them to other analysis tools
D. SPAN ports filter out physical layer errors, making some types of analyses more difficult, and TAPS receives all packets, including physical errors.
Question 15:
A user received a malicious attachment but did not run it. Which category classifies the intrusion?
A. weaponization
B. reconnaissance
C. installation
D. delivery
…
Verify answer:
| Questions: | Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 | Q13 | Q14 | Q15 |
| Answers: | A | A | D | A | C | A | D | D | AB | D | C | A | B | D | D |
These successful candidates who passed the Cisco 200-201 CBROPS Certification Exam in 2023 provided me with a lot of advice, I compiled some and shared them with you! I hope it can help all candidates!
Now, I highly recommend the best Cisco 200-201 CBROPS Certification exam program in 2023: https://www.leads4pass.com/200-201.html (264 Q&A)! More than 90% success rate,
A lighter learning method (PDF+VCE), guarantees 100% passing the exam.
