Online Practice test CompTIA CASP CAS-002 exam questions, 100% real and effective exam questions answers, easy access to CAS-002 dumps enhance your skills and experience, CAS-002 PDF online Download, Meetexams updates valid exam dumps throughout the year for full CAS-002 exam dumps: https://www.leads4pass.com/cas-002.html (Total Questions: 733 Q&A)
[PDF] Free CompTIA CASP CAS-002 pdf dumps download from Google Drive: https://drive.google.com/open?id=1fm0O5FZH2TD4aFhVhdjTexLr1D9SMYCr
[PDF] Free Full CompTIA pdf dumps download from Google Drive: https://drive.google.com/open?id=1cFeWWpiWzsSWZqeuRVlu9NtAcFT4WsiG
(CASP+) Advanced Security Practitioner Certification | CompTIA IT Certifications: https://certification.comptia.org/certifications/comptia-advanced-security-practitioner
Latest effective CompTIA CASP CAS-002 Exam Practice Tests
QUESTION 1
A system administrator needs to develop a policy for when an application server is no longer needed. Which of the
following policies would need to be developed?
A. Backup policy
B. De-provisioning policy
C. Data retention policy
D. Provisioning policy
Correct Answer: C
QUESTION 2
A large organization has gone through several mergers, acquisitions, and de-mergers over the past decade. As a result,
the internal networks have been integrated but have complex dependencies and interactions between systems. Better
integration is needed in order to simplify the underlying complexity. Which of the following is the MOST suitable
integration platform to provide event-driven and standards- based secure software architecture?
A. Service oriented architecture (SOA)
B. Federated identities
C. Object request broker (ORB)
D. Enterprise service bus (ESB)
Correct Answer: D
QUESTION 3
An administrator notices the following file in the Linux server\\’s /tmp directory.
-rwsr-xr-x. 4 root root 234223 Jun 6 22:52 bash*
Which of the following should be done to prevent further attacks of this nature?
A. Never mount the /tmp directory over NFS
B. Stop the rpcidmapd service from running
C. Mount all tmp directories nosuid, noexec
D. Restrict access to the /tmp directory
Correct Answer: C
QUESTION 4
A business wants to start using social media to promote the corporation and to ensure that customers have a good
experience with their products. Which of the following security items should the company have in place before
implementation? (Select TWO).
A. The company must dedicate specific staff to act as social media representatives of the company.
B. All staff needs to be instructed in the proper use of social media in the work environment.
C. Senior staff blogs should be ghost written by marketing professionals.
D. The finance department must provide a cost benefit analysis for social media.
E. The security policy needs to be reviewed to ensure that social media policy is properly implemented.
F. The company should ensure that the company has sufficient bandwidth to allow for social media traffic.
Correct Answer: AE
QUESTION 5
Company XYZ is in negotiations to acquire Company ABC for $1.2millon. Due diligence activities have uncovered
systemic security issues in the flagship product of Company ABC. It has been established that a complete product
rewrite would be needed with average estimates indicating a cost of $1.6millon. Which of the following approaches
should the risk manager of Company XYZ recommend?
A. Transfer the risk
B. Accept the risk
C. Mitigate the risk
D. Avoid the risk
Correct Answer: D
QUESTION 6
CORRECT TEXT
An administrator wants to install a patch to an application. Given the scenario, download, verify and install the patch in
the most secure manner.
Instructions: The last install that is completed will be the final submission.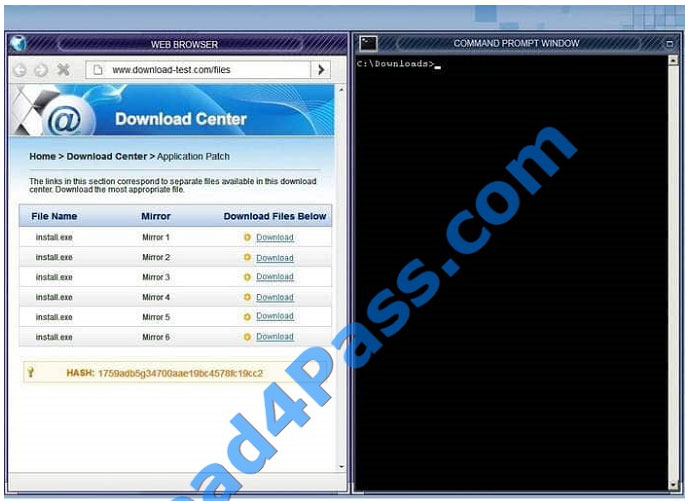
 Correct Answer:
Correct Answer:
Review the for full solution of this exam.
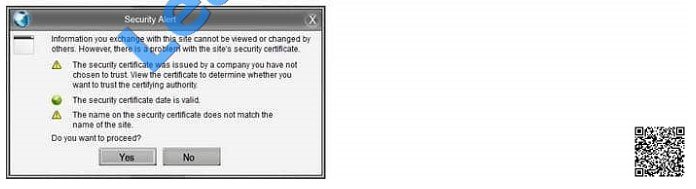
In this case the second link should be used (This may vary in actual exam). The first link showed the following error so it
should not be used. 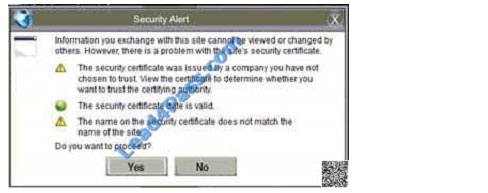
Also, Two of the link choices used HTTP and not HTTPS as shown when hovering over the links as shown: 
Since we need to do this in the most secure manner possible, they should not be used.
Finally, the second link was used and the MD5 utility of MD5sum should be used on the install.exe file as shown. Make
sure that the hash matches. 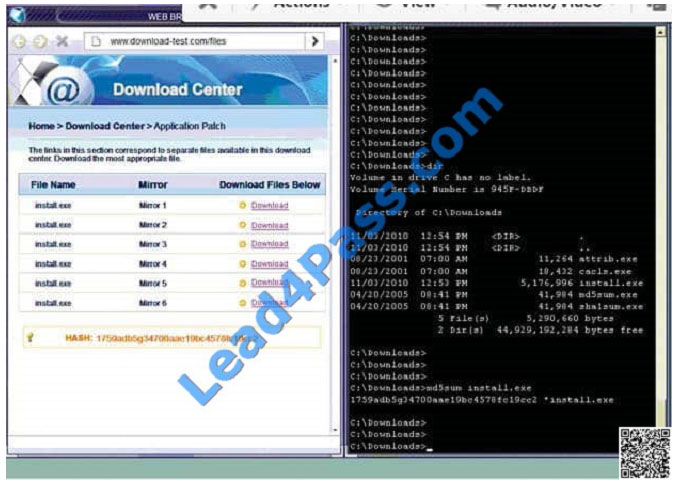 Finally, type in install.exe to install it and make sure there are no signature verification errors.
Finally, type in install.exe to install it and make sure there are no signature verification errors.
QUESTION 7
An educational institution would like to make computer labs available to remote students. The labs are used for various
IT networking, security, and programming courses. The requirements are:
1.
Each lab must be on a separate network segment.
2.
Labs must have access to the Internet, but not other lab networks.
3.
Student devices must have network access, not simple access to hosts on the lab networks.
4.
Students must have a private certificate installed before gaining access.
5.
Servers must have a private certificate installed locally to provide assurance to the students.
6.
All students must use the same VPN connection profile.
Which of the following components should be used to achieve the design in conjunction with directory services?
A. L2TP VPN over TLS for remote connectivity, SAML for federated authentication, firewalls between each lab segment
B. SSL VPN for remote connectivity, directory services groups for each lab group, ACLs on routing equipment
C. IPSec VPN with mutual authentication for remote connectivity, RADIUS for authentication, ACLs on network
equipment
D. Cloud service remote access tool for remote connectivity, OAuth for authentication, ACL on routing equipment
Correct Answer: C
QUESTION 8
The security team for Company XYZ has determined that someone from outside the organization has obtained sensitive
information about the internal organization by querying the external DNS server of the company. The security manager
is tasked with making sure this problem does not occur in the future. How would the security manager address this
problem?
A. Implement a split DNS, only allowing the external DNS server to contain information about domains that only the
outside world should be aware, and an internal DNS server to maintain authoritative records for internal systems.
B. Implement a split DNS, only allowing the external DNS server to contain information about internal domain resources
that the outside world would be interested in, and an internal DNS server to maintain authoritative records for internal
systems.
C. Implement a split DNS, only allowing the external DNS server to contain information about domains that only the
outside world should be aware, and an internal DNS server to maintain non-authoritative records for external systems.
D. Implement a split DNS, only allowing the internal DNS server to contain information about domains the outside world
should be aware of, and an external DNS server to maintain authoritative records for internal systems.
Correct Answer: A
QUESTION 9
At 9:00 am each morning, all of the virtual desktops in a VDI implementation become extremely slow and/ or
unresponsive. The outage lasts for around 10 minutes, after which everything runs properly again. The administrator
has traced the problem to a lab of thin clients that are all booted at 9:00 am each morning. Which of the following is the
MOST likely cause of the problem and the BEST solution? (Select TWO).
A. Add guests with more memory to increase capacity of the infrastructure.
B. A backup is running on the thin clients at 9am every morning.
C. Install more memory in the thin clients to handle the increased load while booting.
D. Booting all the lab desktops at the same time is creating excessive I/O.
E. Install 10-Gb uplinks between the hosts and the lab to increase network capacity.
F. Install faster SSD drives in the storage system used in the infrastructure.
G. The lab desktops are saturating the network while booting.
H. The lab desktops are using more memory than is available to the host systems.
Correct Answer: DF
QUESTION 10
A system worth $100,000 has an exposure factor of eight percent and an ARO of four. Which of the following figures is
the system\\’s SLE?
A. $2,000
B. $8,000
C. $12,000
D. $32,000
Correct Answer: B
QUESTION 11
A security architect is assigned to a major software development project. The software development team has a history
of writing bug prone, inefficient code, with multiple security flaws in every release. The security architect proposes
implementing secure coding standards to the project manager. The secure coding standards will contain detailed
standards for:
A. error handling, input validation, memory use and reuse, race condition handling, commenting, and preventing typical
security problems.
B. error prevention, requirements validation, memory use and reuse, commenting typical security problems, and testing
code standards.
C. error elimination, trash collection, documenting race conditions, peer review, and typical security problems.
D. error handling, input validation, commenting, preventing typical security problems, managing customers, and
documenting extra requirements.
Correct Answer: A
QUESTION 12
The senior security administrator wants to redesign the company DMZ to minimize the risks associated with both
external and internal threats. The DMZ design must support security in depth, change management and configuration
processes, and support incident reconstruction. Which of the following designs BEST supports the given requirements?
A. A dual firewall DMZ with remote logging where each firewall is managed by a separate administrator.
B. A single firewall DMZ where each firewall interface is managed by a separate administrator and logging to the cloud.
C. A SaaS based firewall which logs to the company\\’s local storage via SSL, and is managed by the change control
team.
D. A virtualized firewall, where each virtual instance is managed by a separate administrator and logging to the same
hardware.
Correct Answer: A
QUESTION 13
A popular commercial virtualization platform allows for the creation of virtual hardware. To virtual machines, this virtual
hardware is indistinguishable from real hardware. By implementing virtualized TPMs, which of the following trusted
system concepts can be implemented?
A. Software-based root of trust
B. Continuous chain of trust
C. Chain of trust with a hardware root of trust D. Software-based trust anchor with no root of trust
Correct Answer: C
QUESTION 14
An organization uses IP address block 203.0.113.0/24 on its internal network. At the border router, the network
administrator sets up rules to deny packets with a source address in this subnet from entering the network, and to deny
packets with a destination address in this subnet from leaving the network. Which of the following is the administrator
attempting to prevent?
A. BGP route hijacking attacks
B. Bogon IP network traffic
C. IP spoofing attacks
D. Man-in-the-middle attacks
E. Amplified DDoS attacks
Correct Answer: C
QUESTION 15
A bank provides single sign on services between its internally hosted applications and externally hosted CRM. The
following sequence of events occurs:
1.
The banker accesses the CRM system, a redirect is performed back to the organization\\’s internal systems.
2.
A lookup is performed of the identity and a token is generated, signed and encrypted.
3.
A redirect is performed back to the CRM system with the token.
4.
The CRM system validates the integrity of the payload, extracts the identity and performs a lookup.
5.
If the banker is not in the system and automated provisioning request occurs.
6.
The banker is authenticated and authorized and can access the system. This is an example of which of the following?
A. Service provider initiated SAML 2.0
B. Identity provider initiated SAML 1.0
C. OpenID federated single sign on
D. Service provider initiated SAML 1.1
Correct Answer: A
QUESTION 16
The security administrator has just installed an active\passive cluster of two firewalls for enterprise perimeter defense of
the corporate network. Stateful firewall inspection is being used in the firewall implementation. There have been
numerous reports of dropped connections with external clients.
Which of the following is MOST likely the cause of this problem?
A. TCP sessions are traversing one firewall and return traffic is being sent through the secondary firewall and sessions
are being dropped.
B. TCP and UDP sessions are being balanced across both firewalls and connections are being dropped because the
session IDs are not recognized by the secondary firewall.
C. Prioritize UDP traffic and associated stateful UDP session information is traversing the passive firewall causing the
connections to be dropped.
D. The firewall administrator connected a dedicated communication cable between the firewalls in order to share a
single state table across the cluster causing the sessions to be dropped.
Correct Answer: A
QUESTION 17
An internal committee comprised of the facilities manager, the physical security manager, the network administrator,
and a member of the executive team has been formed to address a recent breach at a company\\’s data center. It was
discovered that during the breach, an HVAC specialist had gained entry to an area that contained server farms holding
sensitive financial data. Although the HVAC specialist was there to fix a legitimate issue, the investigation concluded
security be provided for the two entry and exit points for the server farm. Which of the following should be implemented
to accomplish the recommendations of the investigation?
A. Implement a policy that all non-employees should be escorted in the data center.
B. Place a mantrap at the points with biometric security.
C. Hire an HVAC person for the company, eliminating the need for external HVAC people.
D. Implement CCTV cameras at both points.
Correct Answer: B
QUESTION 18
A recently hired security administrator is advising developers about the secure integration of a legacy in- house
application with a new cloud based processing system. The systems must exchange large amounts of fixed format data
such as names, addresses, and phone numbers, as well as occasional chunks of data in unpredictable formats. The
developers want to construct a new data format and create custom tools to parse and process the data. The security
administrator instead suggests that the developers:
A. Create a custom standard to define the data.
B. Use well formed standard compliant XML and strict schemas.
C. Only document the data format in the parsing application code.
D. Implement a de facto corporate standard for all analyzed data.
Correct Answer: B
QUESTION 19
In developing a new computing lifecycle process for a large corporation, the security team is developing the process for
decommissioning computing equipment. In order to reduce the potential for data leakage, which of the following should
the team consider? (Select TWO).
A. Erase all files on drive
B. Install of standard image
C. Remove and hold all drives
D. Physical destruction
E. Drive wipe
Correct Answer: DE
QUESTION 20
An enterprise must ensure that all devices that connect to its networks have been previously approved. The solution
must support dual factor mutual authentication with strong identity assurance. In order to reduce costs and
administrative overhead, the security architect wants to outsource identity proofing and second factor digital delivery to
the third party. Which of the following solutions will address the enterprise requirements?
A. Implementing federated network access with the third party.
B. Using a HSM at the network perimeter to handle network device access.
C. Using a VPN concentrator which supports dual factor via hardware tokens.
D. Implementing 802.1x with EAP-TTLS across the infrastructure.
Correct Answer: D
QUESTION 21
The helpdesk is receiving multiple calls about slow and intermittent Internet access from the finance department. The
following information is compiled:
Caller 1, IP 172.16.35.217, NETMASK 255.255.254.0
Caller 2, IP 172.16.35.53, NETMASK 255.255.254.0
Caller 3, IP 172.16.35.173, NETMASK 255.255.254.0
All callers are connected to the same switch and are routed by a router with five built-in interfaces. The upstream router
interface\\’s MAC is 00-01-42-32-ab-1a
A packet capture shows the following:
09:05:15.934840 arp reply 172.16.34.1 is-at 00:01:42:32:ab:1a (00:01:42:32:ab:1a)
09:06:16.124850 arp reply 172.16.34.1 is-at 00:01:42:32:ab:1a (00:01:42:32:ab:1a)
09:07:25.439811 arp reply 172.16.34.1 is-at 00:01:42:32:ab:1a (00:01:42:32:ab:1a)
09:08:10.937590 IP 172.16.35.1 > 172.16.35.255: ICMP echo request, id 2305, seq 1, length 65534
09:08:10.937591 IP 172.16.35.1 > 172.16.35.255: ICMP echo request, id 2306, seq 2, length 65534
09:08:10.937592 IP 172.16.35.1 > 172.16.35.255: ICMP echo request, id 2307, seq 3, length 65534
Which of the following is occurring on the network?
A. A man-in-the-middle attack is underway on the network.
B. An ARP flood attack is targeting at the router.
C. The default gateway is being spoofed on the network.
D. A denial of service attack is targeting at the router.
Correct Answer: D
QUESTION 22
An administrator receives reports that the network is running slow for users connected to a certain switch. Viewing the
network traffic, the administrator reviews the following:
18:51:59.042108 IP linuxwksta.55467 andgt; dns.company.com.domain: 39462+ PTR? 222.17.4.10.in-addr.arpa. (42)
18:51:59.055732 IP dns.company.com.domain andgt; linuxwksta.55467: 39462 NXDomain 0/0/0 (42)
18:51:59.055842 IP linuxwksta.48287 andgt; dns.company.com.domain: 46767+ PTR? 255.19.4.10.in-addr.arpa. (42)
18:51:59.069816 IP dns.company.com.domain andgt; linuxwksta.48287: 46767 NXDomain 0/0/0 (42)
18:51:59.159060 IP linuxwksta.42491 andgt; 10.4.17.72.iscsi-target: Flags [P.], seq 1989625106:1989625154, ack
2067334822, win 1525, options [nop,nop,TS val 16021424 ecr 215646227], length 48
18:51:59.159145 IP linuxwksta.48854 andgt; dns.company.com.domain: 3834+ PTR? 72.17.4.10.in-addr.arpa. (41)
18:51:59.159314 IP 10.4.17.72.iscsi-target andgt; linuxwksta.42491: Flags [P.], seq 1:49, ack 48, win 124, options
[nop,nop,TS val 215647479 ecr 16021424], length 48
18:51:59.159330 IP linuxwksta.42491 andgt; 10.4.17.72.iscsi-target: Flags [.], ack 49, win 1525, options [nop,nop,TS val
16021424 ecr 215647479], length 0
18:51:59.165342 IP dns.company.com.domain andgt; linuxwksta.48854: 3834 NXDomain 0/0/0 (41)
18:51:59.397461 ARP, Request who-has 10.4.16.58 tell 10.4.16.1, length 46
18:51:59.397597 IP linuxwksta.37684 andgt; dns.company.com.domain: 15022+ PTR? 58.16.4.10.in-addr.arpa. (41)
Given the traffic report, which of the following is MOST likely causing the slow traffic?
A. DNS poisoning
B. Improper network zoning
C. ARP poisoning
D. Improper LUN masking
Correct Answer: B
QUESTION 23
A penetration tester is assessing a mobile banking application. Man-in-the-middle attempts via a HTTP intercepting
proxy are failing with SSL errors. Which of the following controls has likely been implemented by the developers?
A. SSL certificate revocation
B. SSL certificate pinning
C. Mobile device root-kit detection
D. Extended Validation certificates
Correct Answer: B
QUESTION 24
A Chief Financial Officer (CFO) has raised concerns with the Chief Information Security Officer (CISO) because money
has been spent on IT security infrastructure, but corporate assets are still found to be vulnerable. The business recently
funded a patch management product and SOE hardening initiative. A third party auditor reported findings against the
business because some systems were missing patches. Which of the following statements BEST describes this
situation?
A. The CFO is at fault because they are responsible for patching the systems and have already been given patch
management and SOE hardening products.
B. The audit findings are invalid because remedial steps have already been applied to patch servers and the
remediation takes time to complete.
C. The CISO has not selected the correct controls and the audit findings should be assigned to them instead of the
CFO.
D. Security controls are generally never 100% effective and gaps should be explained to stakeholders and managed
accordingly.
Correct Answer: D
QUESTION 25
There has been a recent security breach which has led to the release of sensitive customer information. As part of
improving security and reducing the disclosure of customer data, a training company has been employed to educate
staff. Which of the following should be the primary focus of the privacy compliance training program?
A. Explain how customer data is gathered, used, disclosed, and managed.
B. Remind staff of the company\\’s data handling policy and have staff sign an NDA.
C. Focus on explaining the “how” and “why” customer data is being collected.
D. Republish the data classification and the confidentiality policy.
Correct Answer: A
QUESTION 26
To prevent a third party from identifying a specific user as having previously accessed a service provider through an
SSO operation, SAML uses which of the following?
A. Transient identifiers
B. SOAP calls
C. Discovery profiles
D. Security bindings
Correct Answer: A
QUESTION 27
A Chief Information Security Officer (CISO) of a major consulting firm has significantly increased the company\\’s
security posture; however, the company is still plagued by data breaches of misplaced assets. These data breaches as
a result have led to the compromise of sensitive corporate and client data on at least 25 occasions. Each employee in
the company is provided a laptop to perform company business. Which of the following actions can the CISO take to
mitigate the breaches?
A. Reload all user laptops with full disk encryption software immediately.
B. Implement full disk encryption on all storage devices the firm owns.
C. Implement new continuous monitoring procedures.
D. Implement an open source system which allows data to be encrypted while processed.
Correct Answer: B
QUESTION 28
Ann, a systems engineer, is working to identify an unknown node on the corporate network. To begin her investigative
work, she runs the following nmap command string:
user@hostname:~$ sudo nmap -O 192.168.1.54
Based on the output, nmap is unable to identify the OS running on the node, but the following ports are open on the
device:
TCP/22
TCP/111
TCP/512-514
TCP/2049
TCP/32778
Based on this information, which of the following operating systems is MOST likely running on the unknown node?
A. Linux
B. Windows
C. Solaris
D. OSX
Correct Answer: C
QUESTION 29
An external auditor has found that IT security policies in the organization are not maintained and in some cases are
nonexistent. As a result of the audit findings, the CISO has been tasked with the objective of establishing a mechanism
to manage the lifecycle of IT security policies. Which of the following can be used to BEST achieve the CISO\\’s
objectives?
A. CoBIT
B. UCF
C. ISO 27002
D. eGRC
Correct Answer: D
QUESTION 30
A developer is determining the best way to improve security within the code being developed. The developer is focusing
on input fields where customers enter their credit card details. Which of the following techniques, if implemented in the
code, would be the MOST effective in protecting the fields from malformed input?
A. Client side input validation
B. Stored procedure
C. Encrypting credit card details
D. Regular expression matching
Correct Answer: D
QUESTION 31
A completely new class of web-based vulnerabilities has been discovered. Claims have been made that all common
web-based development frameworks are susceptible to attack. Proof-of-concept details have emerged on the Internet. A
security advisor within a company has been asked to provide recommendations on how to respond quickly to these
vulnerabilities. Which of the following BEST describes how the security advisor should respond?
A. Assess the reliability of the information source, likelihood of exploitability, and impact to hosted data. Attempt to
exploit via the proof-of-concept code. Consider remediation options.
B. Hire an independent security consulting agency to perform a penetration test of the web servers. Advise
management of any `high\\’ or `critical\\’ penetration test findings and put forward recommendations for mitigation.
C. Review vulnerability write-ups posted on the Internet. Respond to management with a recommendation to wait until
the news has been independently verified by software vendors providing the web application software.
D. Notify all customers about the threat to their hosted data. Bring the web servers down into “maintenance mode” until
the vulnerability can be reliably mitigated through a vendor patch.
Correct Answer: A
QUESTION 32
An assessor identifies automated methods for identifying security control compliance through validating sensors at the
endpoint and at Tier 2. Which of the following practices satisfy continuous monitoring of authorized information
systems?
A. Independent verification and validation
B. Security test and evaluation
C. Risk assessment
D. Ongoing authorization
Correct Answer: D
QUESTION 33
A developer has implemented a piece of client-side JavaScript code to sanitize a user\\’s provided input to a web page
login screen. The code ensures that only the upper case and lower case letters are entered in the username field, and
that only a 6-digit PIN is entered in the password field. A security administrator is concerned with the following web
server log:
10.235.62.11 — [02/Mar/2014:06:13:04] andquot;GET /site/script.php?user=adminandamp;pass=pass%20or%201=1
HTTP/1.1andquot; 200 5724
Given this log, which of the following is the security administrator concerned with and which fix should be implemented
by the developer?
A. The security administrator is concerned with nonprintable characters being used to gain administrative access, and
the developer should strip all nonprintable characters.
B. The security administrator is concerned with XSS, and the developer should normalize Unicode characters on the
browser side.
C. The security administrator is concerned with SQL injection, and the developer should implement server side input
validation.
D. The security administrator is concerned that someone may log on as the administrator, and the developer should
ensure strong passwords are enforced.
Correct Answer: C
QUESTION 34
Executive management is asking for a new manufacturing control and workflow automation solution. This application will
facilitate management of proprietary information and closely guarded corporate trade secrets.
The information security team has been a part of the department meetings and come away with the following notes:
-Human resources would like complete access to employee data stored in the application. They would like automated
data interchange with the employee management application, a cloud-based SaaS application.
-Sales is asking for easy order tracking to facilitate feedback to customers.
-Legal is asking for adequate safeguards to protect trade secrets. They are also concerned with data ownership
questions and legal jurisdiction.
-Manufacturing is asking for ease of use. Employees working the assembly line cannot be bothered with additional steps
or overhead. System interaction needs to be quick and easy.
-Quality assurance is concerned about managing the end product and tracking overall performance of the product being
produced. They would like read-only access to the entire workflow process for monitoring and baselining.
The favored solution is a user friendly software application that would be hosted onsite. It has extensive ACL
functionality, but also has readily available APIs for extensibility. It supports read-only access, kiosk automation, custom
fields, and
data encryption.
Which of the following departments\\’ request is in contrast to the favored solution?
A. Manufacturing
B. Legal
C. Sales
D. Quality assurance
E. Human resources
Correct Answer: E
QUESTION 35
VPN users cannot access the active FTP server through the router but can access any server in the data center.
Additional network information:
DMZ network -192.168.5.0/24 (FTP server is 192.168.5.11)
VPN network -192.168.1.0/24
Datacenter -192.168.2.0/24
User network – 192.168.3.0/24
HR network -192.168.4.0/24\
Traffic shaper configuration:
VLAN Bandwidth Limit (Mbps)
VPN50
User175
HR250
Finance250
Guest0
Router ACL:
ActionSourceDestination
Permit192.168.1.0/24192.168.2.0/24
Permit192.168.1.0/24192.168.3.0/24
Permit192.168.1.0/24192.168.5.0/24
Permit192.168.2.0/24192.168.1.0/24
Permit192.168.3.0/24192.168.1.0/24
Permit192.168.5.1/32192.168.1.0/24
Deny192.168.4.0/24192.168.1.0/24
Deny192.168.1.0/24192.168.4.0/24
Denyanyany
Which of the following solutions would allow the users to access the active FTP server?
A. Add a permit statement to allow traffic from 192.168.5.0/24 to the VPN network
B. Add a permit statement to allow traffic to 192.168.5.1 from the VPN network
C. IPS is blocking traffic and needs to be reconfigured
D. Configure the traffic shaper to limit DMZ traffic
E. Increase bandwidth limit on the VPN network
Correct Answer: A
QUESTION 36
A growing corporation is responding to the needs of its employees to access corporate email and other resources while
traveling. The company is implementing remote access for company laptops. Which of the following security systems
should be implemented for remote access? (Select TWO).
A. Virtual Private Network
B. Secure Sockets Layer for web servers
C. Network monitoring
D. Multifactor authentication for users
E. Full disk encryption
F. Intrusion detection systems
Correct Answer: AD
QUESTION 37
A large financial company has a team of security-focused architects and designers that contribute into broader IT
architecture and design solutions. Concerns have been raised due to the security contributions having varying levels of
quality and consistency. It has been agreed that a more formalized methodology is needed that can take business
drivers, capabilities, baselines, and re-usable patterns into account. Which of the following would BEST help to achieve
these objectives?
A. Construct a library of re-usable security patterns
B. Construct a security control library
C. Introduce an ESA framework
D. Include SRTM in the SDLC
Correct Answer: C
QUESTION 38
A security consultant is conducting a network assessment and wishes to discover any legacy backup Internet
connections the network may have. Where would the consultant find this information and why would it be valuable?
A. This information can be found in global routing tables, and is valuable because backup connections typically do not
have perimeter protection as strong as the primary connection.
B. This information can be found by calling the regional Internet registry, and is valuable because backup connections
typically do not require VPN access to the network.
C. This information can be found by accessing telecom billing records, and is valuable because backup connections
typically have much lower latency than primary connections.
D. This information can be found by querying the network\\’s DNS servers, and is valuable because backup DNS
servers typically allow recursive queries from Internet hosts.
Correct Answer: A
QUESTION 39
A Security Manager is part of a team selecting web conferencing systems for internal use. The system will only be used
for internal employee collaboration. Which of the following are the MAIN concerns of the security manager? (Select
THREE).
A. Security of data storage
B. The cost of the solution
C. System availability
D. User authentication strategy
E. PBX integration of the service
F. Operating system compatibility
Correct Answer: ACD
QUESTION 40
Company policy requires that all company laptops meet the following baseline requirements: Software requirements:
Antivirus Anti-malware Anti-spyware Log monitoring Full-disk encryption Terminal services enabled for RDP
Administrative access for local users
Hardware restrictions: Bluetooth disabled FireWire disabled WiFi adapter disabled Ann, a web developer, reports
performance issues with her laptop and is not able to access any network resources. After further investigation, a bootkit
was discovered and it was trying to access external websites. Which of the following
hardening techniques should be applied to mitigate this specific issue from reoccurring? (Select TWO).
A. Group policy to limit web access
B. Restrict VPN access for all mobile users
C. Remove full-disk encryption
D. Remove administrative access to local users
E. Restrict/disable TELNET access to network resources
F. Perform vulnerability scanning on a daily basis
G. Restrict/disable USB access
Correct Answer: DG
We offer more ways to make it easier for everyone to learn, and YouTube is the best tool in the video. Follow channels: https://www.youtube.com/channel/UCXg-xz6fddo6wo1Or9eHdIQ/videos get more useful exam content.
Latest CompTIA CASP CAS-002 YouTube videos:
Meetexams updates the latest effective exam dumps throughout the year (cisco,microsoft,oracle,CompTIA,comptia,VMware …) ! Share 40 valid CompTIA CASP CAS-002 exam dumps for free to get the full CAS-002 Dumps: https://www.leads4pass.com/cas-002.html (Total Questions:733 Q&As)
[PDF] Free CompTIA CASP CAS-002 pdf dumps download from Google Drive: https://drive.google.com/open?id=1fm0O5FZH2TD4aFhVhdjTexLr1D9SMYCr
[PDF] Free Full CompTIA pdf dumps download from Google Drive: https://drive.google.com/open?id=1cFeWWpiWzsSWZqeuRVlu9NtAcFT4WsiG
Lead4pass Promo Code 12% Off
related: https://www.dumpinside.com/cisco-ccna-data-center-640-916-dumps-exam/
